Active Directory integration
Qlik Catalog enables enterprises to dynamically sync Qlik Catalog-managed security with Active Directory (AD) identity services and domain management. LDAP protocol is used to connect to and obtain information from AD.
Qlik Catalog does not allow updates to the external AD database. Fields are provided for connection description, location/credentials, and parameters to define search criteria for objects of interest.
This integration allows Qlik Catalog Administrators to:
- Obtain summary counts of groups and users from AD.
- Update with AD groups (and users) either: one-time immediately, on a schedule set manually with calendar feature, or set on a recurrent user-defined schedule with a Quartz cron expression..
- Define, edit, disable AD synchronization schedule.
- Select whether the connection is to be made with SSL encryption.
- View, save, delete, edit all connections.
- View all logs relevant to synchronization tasks.
Qlik Catalog allows a mix of Active Directory, Kerberos, and local users. User names and login credentials reflect this status. AD users log in with fully a qualified name at(@) the AD domain name (e.g., joe@bestcompany.com or joe@ad.bestcompany.net) and AD password or their user name with AD domain dropdown selection. Local user login name and password credentials do not change. Local users log in with credentials and choose none for domain.
AD and Local Environment (Group and User) names
Users
An AD username is always appended with the domain suffix. Username 'bbishop' will be appended to become 'bbishop@ad.catalogdata.net' when Qlik Catalog syncs with Active Directory.
A locally created user 'bbishop' and an AD user 'bbishop@ad.podiumdata.net' are considered distinct and will not conflict. The Active Directory user will be successfully created alongside the locally-created user when Qlik Catalog syncs with AD.
Groups
An Active Directory group will not be appended with a domain suffix so 'BriansGroup' will be imported as BriansGroup — If a group with title BriansGroup already exists in the Qlik Catalog metadata, the AD group will not be imported. If the administrator wants to keep both groups, they should rename the existing group then run the AD sync (example: BriansGroup1).
Users and groups are case-sensitive, so BriansGroup and briansgroup are distinct groups.
Creating an AD synchronization
-
To sync Qlik Catalog with AD select Add New Domain.
Add New Domain
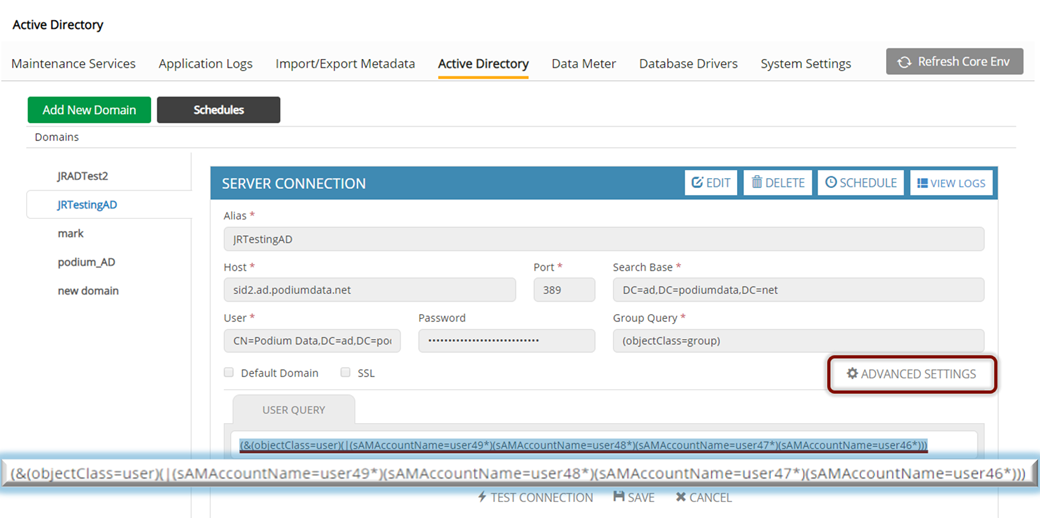
The following fields are required to sync Qlik Catalog with an AD Database via LDAP server connection:
- Alias: Alternate name for Host/LDAP Server.
- Host: LDAP Server URL, a fully qualified domain name (ex. DC01.domainname.com).
- Port: The port that has been configured for the LDAP Server.
- Search Base: LDAP Search Base (the directory being searched, e.g., ad.qdcdata.net).
- User: LDAP Bind User Distinguished Name (user name configured for LDAP authentication).
- Password: LDAP Bind Password (password configured for LDAP authentication).
- Group Query: LDAP Select query for group object(s) of interest.
- Default domain (Checkbox): Check this box to set LDAP Server as default domain. Note: There can only be one default domain. This facilitates easier login for users in future releases.
- SSL (Checkbox): Check to enable Secure Sockets Layer (SSL) encryption of LDAP client/server communication.
-
Once a connection has been successfully established, select Schedule.
A pop-up box will appear with two radio buttons next to One-Time Immediate or Recurring:
- One Time Immediate will begin an AD synchronization.
- Recurring will prompt the user to select Choose your Schedule, or Custom Schedule. Users can opt to define a schedule through calendar scheduler or enter a Quartz cron expression to customize an automated schedule.
-
To choose a One Time Immediate synchronization, click on the radio button indicated, Then, choose Run to start the synchronization with AD. The system displays results (see figure, below), with headings:
- View Summary displays summary counts of groups and users from AD.
- View Synchronization Results lists the users and groups returned by the LDAP query.
- View Updates displays the updates made to Qlik Catalog.
To complete the process, click Finish. The system will display a success message.
- To use a Calendar Scheduler for synchronization, choose Recurring, then choose the radio button Choose Your Schedule and enter appropriate field information.
-
To use a Quartz cron expression to create an automated schedule, choose Recurring, then select the radio button next to Custom Schedule. Complete the entry with the Quartz cron expression. Refer to the following link for guidelines to create a Quartz cron expression:
http://www.quartz-scheduler.org/documentation/quartz-2.3.0/tutorials/crontrigger.html
To initiate scheduling, click Finish.
Preview synchronization results
After defining a schedule for AD synchronization users can preview the updates. This view displays what is in AD for the User/Group Queries at that time; actual results are subject to changes in AD.
AD domain commands
Delete Domain
Highlight the domain to be deleted in the left sidebar and select Delete Domain.
View Logs
Highlight the domain in the left bar sidebar and select View Logs.
Edit
The Edit command will clear all locked (gray) fields and allow authorized users to edit the fields. To complete the edits: Highlight the domain to be edited in the left sidebar and select Edit.
- Choose Test Connection to make sure the edits preserve the server connection (the system displays a success message or error message).
- Choose Cancel to lock the fields without changes.
- To save the edits, choose Save.
Disable or enable controls are located at the bottom of the screen, they indicate whether synchronization is active; Disable Schedule will display when synchronization is scheduled. Enable Schedule displays when a schedule is in place but not active.
Enable Schedule or Disable Schedule
Advanced settings
User Query
This query provides the option to create a more exclusive query overriding the dynamically generated user query based on the group query results.
This query returns only users existing in the groups resulting from group query.
Create a more exclusive query
Rules for import and filter of users and groups that already exist in Qlik Catalog upon AD sync
When Qlik Catalog runs a query on Active Directory, all groups and users from AD that are returned from the query are filtered according to the following rules:
-
Groups: If a group exists under a different AD connection or exists locally then the group is ignored and it is not added to the system again and is not included in the summary count.
-
Users: If a user exists under a different AD connection or exists locally then the user is ignored and is not added to the system again and is not included in the summary count.
