Audit trails
The information provided in an Audit Trail can be leveraged for user accountability, reconstruction of events, intrusion detection, and other operational issues. As such, Audit Trails are an indispensable tool for regulatory compliance (e.g. SOX).
For operations performed by users with Operator privileges or later, the Compose Audit Trail shows which user performed the operation, when it was performed, and on which objects.
By default, Compose retains audit files for one week or until they reach a total size of 100 MB (10 files). You can change these settings through the command line interface (CLI) as described in Exporting Audit Trail files below.
Audit Trail files are located in the following folder:
<Installation_Directory>\data\AuditTrail\audit_service
You can also export an audit trail file for a specific time range, as described in Exporting Audit Trail files.
Audit trail information
Audit Trail files provide all or some of the following information:
- Timestamp - The time when the row was inserted into the Audit Trail.
- User - The user that performed the operation.
- Node - The IP of the server on which the operation was performed.
- Requested Action - The API method/function that was called.
- Required Permission - The minimum role of the user that can perform the operation.
- Effective Permission - The actual role of the user that performed the operation.
- Security Result - Whether the user is allowed to perform the operation.
- Action Result - The completion status of the operation (success of failure).
- Error Message - The error message if the operation failed.
- Task - The name of the task where relevant.
- Notification - The notification defined for the operation (if defined).
-
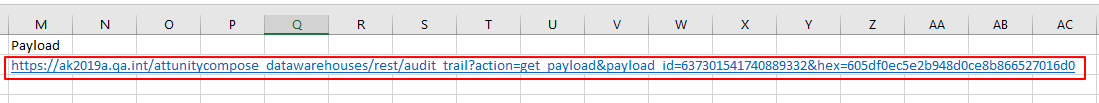
Payload - A URL. To view payload information, simply copy the link from the Payload column and paste it into your browser's address bar.
Payloads for some operations (e.g. RegisterLicense) contain sensitive information and need to be decoded. For information on decoding payloads, see Decoding an encoded payload.
- Project Name - The name of the Compose project.
Audit Trail files are compressed and tamper-protected.
Exporting Audit Trail files
You can export an audit trail file with a record of activity for a specific time range. In Compose, there are two way of doing this:.
- Using the management console
- Using the CLI
You can also export audit trails using the ExportAuditTrail API method. For further information, see the Qlik Enterprise Manager Help and API Guide.
Exporting an Audit Trail file via the management console
You can use the Compose management console to export the audit trail as a CSV file.
To do this:
-
From the Management drop-down menu, select Audit Trail. The Audit Trail window opens.
- From the Time Range drop-down list, select the desired time range. If you select Custom, set From and To values as well.
-
Click Generate.
Depending on your browser settings, you will either be prompted for a download location or the file will be downloaded automatically to your preferred location.
Exporting an Audit Trail file via the CLI
You can use the Compose CLI to export the audit trail as a JSON file.
Run the following command from the Compose bin directory:
Command syntax
ComposeCli.exe generate_audit_trail --start_timestamp timestamp [--end_timestamp timestamp] --outfile full_path
Parameters
| Parameter | Description |
|---|---|
| --start_timestamp |
The date and time from which you want the audit trail to start, in UTC format. |
| --end_timestamp |
The date and time on which you want the audit trail to end, in UTC format. When not specified, the file will end at the latest audit trail record. |
| --outfile | The full path to the output file. If the path contains spaces, it should be enclosed in quotation marks. |
Example
ComposeCli.exe generate_audit_trail --start_timestamp 2020-06-30T16:15:00Z --end_timestamp 2020-07-14T16:15:00Z --outfile "C:\compose audit trails\audit.json"
Configuring Audit Trail size and retention
Run the following command from the Composebin directory:
Command syntax
ComposeCtl.exe audit_trail_control --age weeks --size megabytes
Parameters
| Parameter | Description |
|---|---|
| --age |
The number of weeks to retain the audit trail file (default 1 week). |
| --size |
The maximum size of the audit file to retain (default 100 MB). |
Example
ComposeCtl.exe audit_trail_control --age 4 --size 1000
Decoding an encoded payload
Some audit records (e.g. RegisterLicenses) may contain an encoded payload. Encoded payloads are displayed as byte arrays and need to be decoded using Base64.
To decode an encoded stream payload:
-
Locate the payload URL in the audit record.
-
Copy the URL into your browser's address bar and press [Enter]. A byte array will be displayed.
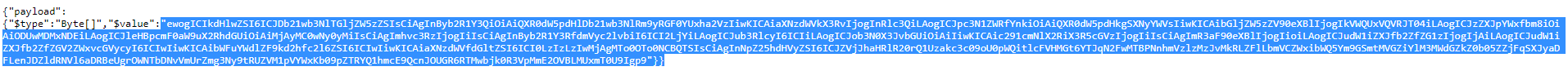
-
Copy the byte array into a Base64 decoder and decode it.
